Configuration Profiles For Persistence Os X
Dec 10, 2014 When I check Profiles in the System Preferences pane, I can see that the settings are indeed listed though. I am doing this with a server running Mac OS X 10.9.5 and OS X Server 3/Profile Manager and my test client is running Mac OS X 10.9.5. To see what profiles are installed, and then remove one, assuming you can sudo to the user, you could try: root$ sudo -u chymb profiles -L chymb1 attribute: profileIdentifier: com.stackexchange.apple.test There are 1 user configuration profiles installed for 'chymb' root$ sudo -u chymb profiles -R -p com.stackexchange.apple.test.
Java ide for mac os sierra. MacOS Sierra was released by Apple in September 2016. Java is compatible with this version, however, few Java issues have been reported on Sierra. We are actively working on identifying and resolving those issues. A few of the issues that we are currently addressing are listed below. JVM throws NullPointerExceptions on macOS Sierra 10.12. Oct 08, 2019 Java is a general-purpose, secure, robust, object-oriented language developed by Sun Microsystems in 1990. Java is portable which means it follows to write once run anywhere paradigm. The latest version is Java 13 which was released on March 2019. This tutorial helps you to install Java 13 latest or Java 11 LTS on macOS Sierra or High Sierra. Eclipse is an integrated development environment used in computer programming, and is the most widely used Java IDE. It contains a base workspace and an extensible plug-in system for customizing the environment. Eclipse was inspired by the Smalltalk-based VisualAge family of integrated development environment (IDE) products. This version of the Arduino IDE for Mac OS X runs only if you already have Java7 or later installed on your computer. Download MAC OS X for Java 7+ (experimental) This guide will help you setting up your Mac if you want to install the experimental version of the Arduino IDE 1.6.1.
- Configuration Profiles For Persistence Os X Mac
- Configuration Profiles For Persistence Os X 12
- Configuration Profiles For Persistence Os X 8
This article is intended for system administrators who set security policy in enterprise environments that require smart card authentication.
Jul 20, 2016 Speakers: Segio Aviles & Jeremy Reichman Configuration profiles are Apple's supported method of changing the default settings in OS X to support educational, corporate,. Jul 20, 2016 Configuration profiles are Apple's supported method of changing the default settings in OS X to support educational, corporate, and organizational needs. Savvy system administrators can take. The Computer Configuration GP will install profiles at the Device Level and is supported for OS X 10.7 and higher. The User Configuration GP will install profiles at the User Level and is supported for OS X 10.9 and higher. Make sure to check the Explain tabs in both GPs for correct usage and deployment.
Enable smart card-only login
Make sure that you carefully follow these steps to ensure that users will be able to log in to the computer.
- Pair a smart card to an admin user account or configure Attribute Matching.
- If you’ve enabled strict certificate checks, install any root certificates or intermediates that are required.
- Confirm that you can log in to an administrator account using a smart card.
- Install a smart-card configuration profile that includes '<key>enforceSmartCard</key><true/>,' as shown in the smart card-only configuration profile below.
- Confirm that you can still log in using a smart card.
For more information about smart card payload settings, see the Apple Configuration Profile Reference.
For more information about using smart card services, see the macOS Deployment Guide or open Terminal and enter man SmartCardServices.
Disable smart card-only authentication
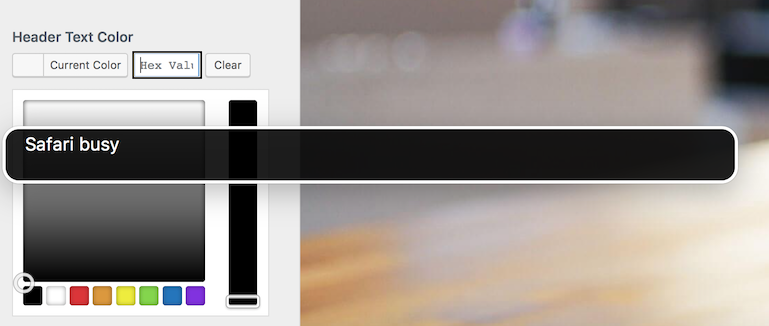
If you manually manage the profiles that are installed on the computer, you can remove the smart card-only profile in two ways. You can use the Profiles pane of System Preferences, or you can use the /usr/bin/profiles command-line tool. For more information, open Terminal and enter man profiles.
Configuration Profiles For Persistence Os X Mac
If your client computers are enrolled in Mobile Device Management (MDM), you can restore password-based authentication. To do this, remove the smart card configuration profile that enables the smart card-only restriction from the client computers.
To prevent users from being locked out of their account, remove the enforceSmartCard profile before you unpair a smart card or disable attribute matching. If a user is locked out of their account, remove the configuration profile to fix the issue.
If you apply the smart card-only policy before you enable smart card-only authentication, a user can get locked out of their computer. To fix this issue, remove the smart card-only policy:
- Turn on your Mac, then immediately press and hold Command-R to start up from macOS Recovery. Release the keys when you see the Apple logo, a spinning globe, or a prompt for a firmware password.
- Select Disk Utility from the Utilities window, then click Continue.
- From the Disk Utility sidebar, select the volume that you're using, then choose File > Mount from the menu bar. (If the volume is already mounted, this option is dimmed.) Then enter your administrator password when prompted.
- Quit Disk Utility.
- Choose Terminal from the Utilities menu in the menu bar.
- Delete the Configuration Profile Repository. To do this, open Terminal and enter the following commands.
In these commands, replace <volumename> with the name of the macOS volume where the profile settings were installed.rm /Volumes/<volumename>/var/db/ConfigurationProfiles/MDM_ComputerPrefs.plistrm /Volumes/<volumename>/var/db/ConfigurationProfiles/.profilesAreInstalledrm /Volumes/<volumename>/var/db/ConfigurationProfiles/Settings/.profilesAreInstalledrm /Volumes/<volumename>/var/db/ConfigurationProfiles/Store/ConfigProfiles.binaryrm /Volumes/<volumename>/var/db/ConfigurationProfiles/Setup/.profileSetupDone - When done, choose Apple () menu > Restart.
- Reinstall all the configuration profiles that existed before you enabled smart card-only authentication.
Configure Secure Shell Daemon (SSHD) to support smart card-only authentication
Users can use their smart card to authenticate over SSH to the local computer or to remote computers that are correctly configured. Follow these steps to configure SSHD on a computer so that it supports smart card authentication.
Update the /etc/ssh/sshd_config file:
- Use the following command to back up the sshd_config file:
sudo cp /etc/ssh/sshd_config /etc/ssh/sshd_config_backup_`date '+%Y-%m-%d_%H:%M'` - In the sshd_config file, change '#ChallengeResponseAuthentication yes' to 'ChallengeResponseAuthentication no' and change '#PasswordAuthentication yes' to '#PasswordAuthentication no.'
Then, use the following commands to restart SSHD:
sudo launchctl stop com.openssh.sshd
sudo launchctl start com.openssh.sshd
If a user wants to authenticate SSH sessions using a smart card, have them follow these steps:
- Use the following command to export the public key from their smart card:
ssh-keygen -D /usr/lib/ssh-keychain.dylib - Add the public key from the previous step to the ~/.ssh/authorized_keys file on the target computer.
- Use the following command to back up the ssh_config file:
sudo cp /etc/ssh/ssh_config /etc/ssh/ssh_config_backup_`date '+%Y-%m-%d_%H:%M'` - In the/etc/ssh/ssh_config file, add the line 'PKCS11Provider=/usr/lib/ssh-keychain.dylib.'
If the user wants to, they can also use the following command to add the private key to their ssh-agent:
ssh-add -s /usr/lib/ssh-keychain.dylib
Enable smart card-only for the SUDO command
Use the following command to back up the /etc/pam.d/sudo file:
sudo cp /etc/pam.d/sudo /etc/pam.d/sudo_backup_`date '+%Y-%m-%d_%H:%M'`
Then, replace all of the contents of the /etc/pam.d/sudo file with the following text:
Enable smart card-only for the LOGIN command
Use the following command to back up the /etc/pam.d/login file:
sudo cp /etc/pam.d/login /etc/pam.d/login_backup_`date '+%Y-%m-%d_%H:%M'`
Then, replace all of the contents of the/etc/pam.d/login file with the following text:
Enable smart card-only for the SU command
Use the following command to back up the /etc/pam.d/su file:
sudo cp /etc/pam.d/su /etc/pam.d/su_backup_`date '+%Y-%m-%d_%H:%M'`
Then, replace all of the contents of the/etc/pam.d/su file with the following text:
Configuration Profiles For Persistence Os X 12
Sample smart card-only configuration profile
Here’s a sample smart card-only configuration profile. You can use it to see the kinds of keys and strings that this type of profile includes.
In iOS and macOS, configuration profiles are XML files that contain settings to manage Wi-Fi, email accounts, passcode options, and many other functions of iPhone, iPod touch, iPad, and Mac devices. To use them, you must have either iOS 4 or later or macOS.
Profiles can be installed through a web page, via email, or by using the iPhone Configuration Utility from Apple. Profiles can also be updated remotely by a mobile device management service.
Configuration Profiles For Persistence Os X 8
To uninstall a configuration profile, see Remove a configuration profile in iOS or macOS.