Outlook For Mac High Sierra 10.13.5
- Jan 15, 2020 Download macOS High Sierra 10.13.5 ISO Image File. Apple has released MacOS 10.13.5 update for Mac users. The new update for macOS includes many bug fixes and minor enhancements. If you are using a MacOS operating system and want to upgrade/update this new version, you can download and install this update from the Apple Store.However, if you do not know how to update the.
- Dec 06, 2017 The macOS High Sierra 10.13.2 update improves the stability, compatibility and security of your Mac, and is recommended for all users. This update:. Improves compatibility with certain third-party USB audio devices. Improves VoiceOver navigation when viewing PDF documents in Preview. Improves compatibility of Braille displays with Mail.
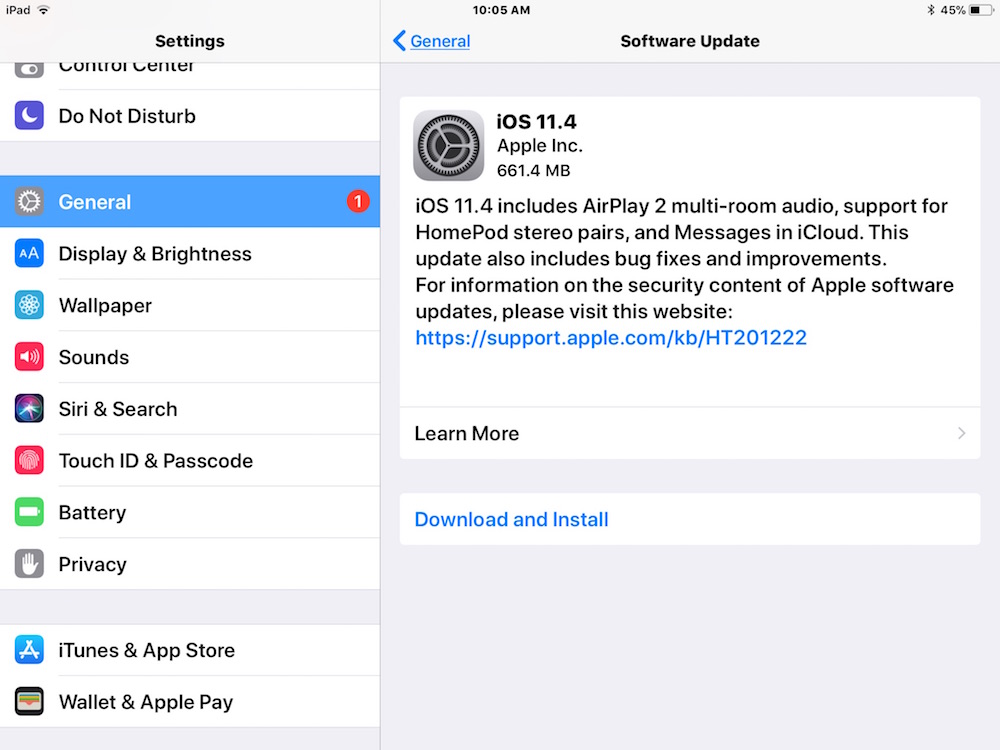
Jun 04, 2018 The High Sierra 10.13.5 update is the fifth major update for macOS High Sierra. This update adds support for Messages in iCloud, which lets you store messages with their attachments in iCloud and free up space on your Mac. Also added is a number of undocumented fixes, improvements, security enhancements to macOS. This is a minor and smooth update and shouldn’t require any.
High Sierra is an update of MacOS which focuses mostly on back-end developments and a higher level of user security. As such, this operating system lays a foundation for future upgrades.
Stay safe
In essence, High Sierra took what was good with Sierra and developed it into a more comprehensive software.
High Sierra emphasizes the already-existing benefits of MacOS previous system, Sierra. There are few bells and whistles, but the changes are noticeable and positive. The Apple file system is the most significant feature it brought. It enables the storage and encryption of a large number of files. Thus, it boosts performance and helps manage device memory issues.
Apple also introduced new formats for video and photos in this version. These formats compress data - that’s a benefit as files can get huge with ever-rising resolutions. They added support for virtual reality headsets as well.
Besides that, when it comes to Safari, Mac search engine, there are some notable improvements with the update. The users can now control annoying auto-play videos, prevent tracking, and more. There are also notification controls, and you will experience a boost in performance, too.
The most noticeable changes took place in Apple’s Photo App, though. It went through a total revamp both visually in its interface and terms of tools and functions available. Many other discreet changes happened all over the system.
Where can you run this program?
If you’re running Sierra on your Mac, you will be able to run this one as well.
Is there a better alternative?
Yes. Mojave, the newest version of MacOS, brought even more improved features to the table. However, if you can’t run it on your device, this is the second best.
Our take
High Sierra is not the shiniest upgrade Apple brought, but it’s one that sets the stage for new upgrades to come. Even out of that context, it’s a great operating system.
Should you download it?
Yes, if your device can support it. The new options and better security settings are worth getting.
10.13
About Apple security updates
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
For more information about security, see the Apple Product Security page. You can encrypt communications with Apple using the Apple Product Security PGP Key.
Apple security documents reference vulnerabilities by CVE-ID when possible.
macOS High Sierra 10.13.6, Security Update 2018-004 Sierra, Security Update 2018-004 El Capitan
Released July 9, 2018
Accounts
Available for: macOS High Sierra 10.13.5
Impact: A malicious application may be able to access local users AppleIDs
Description: A privacy issue in the handling of Open Directory records was addressed with improved indexing.
CVE-2018-4470: Jacob Greenfield of Commonwealth School
Entry added December 10, 2018
AMD
Available for: macOS High Sierra 10.13.5
Impact: A malicious application may be able to determine kernel memory layout
Description: An information disclosure issue was addressed by removing the vulnerable code.
CVE-2018-4289: shrek_wzw of Qihoo 360 Nirvan Team
APFS
Available for: macOS High Sierra 10.13.5
Impact: An application may be able to execute arbitrary code with kernel privileges
Outlook For Mac High Sierra 10.13.55
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2018-4268: Mac working with Trend Micro's Zero Day Initiative
ATS
Available for: macOS High Sierra 10.13.5
Impact: A malicious application may be able to gain root privileges
Description: A type confusion issue was addressed with improved memory handling.
CVE-2018-4285: Mohamed Ghannam (@_simo36)
Bluetooth
Available for: MacBook Pro (15-inch, 2018) and MacBook Pro (13-inch, 2018, Four Thunderbolt 3 Ports)
Other Mac models were addressed with macOS High Sierra 10.13.5.
Impact: An attacker in a privileged network position may be able to intercept Bluetooth traffic
Description: An input validation issue existed in Bluetooth. This issue was addressed with improved input validation.
CVE-2018-5383: Lior Neumann and Eli Biham
Entry added July 23, 2018
CFNetwork
Available for: macOS High Sierra 10.13.5
Impact: Cookies may unexpectedly persist in Safari
Description: A cookie management issue was addressed with improved checks.
CVE-2018-4293: an anonymous researcher
CoreCrypto
Available for: OS X El Capitan 10.11.6, macOS Sierra 10.12.6
Impact: A malicious application may be able to break out of its sandbox
Outlook For Mac High Sierra Download
Description: A memory corruption issue was addressed with improved input validation.
CVE-2018-4269: Abraham Masri (@cheesecakeufo)
CUPS
Available for: OS X El Capitan 10.11.6, macOS Sierra 10.12.6, macOS High Sierra 10.13.5
Impact: An attacker in a privileged position may be able to perform a denial of service attack
Description: A null pointer dereference was addressed with improved validation.
CVE-2018-4276: Jakub Jirasek of Secunia Research at Flexera
Entry added September 25, 2018
DesktopServices
Available for: macOS Sierra 10.12.6
Impact: A local user may be able to view sensitive user information
Description: A permissions issue existed in which execute permission was incorrectly granted. This issue was addressed with improved permission validation.
CVE-2018-4178: Arjen Hendrikse
Intel Graphics Driver
Available for: macOS High Sierra 10.13.5
Best method for capturing time lapse photos sierra mac. Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved input validation.
CVE-2018-4456: Tyler Bohan of Cisco Talos
Entry updated January 22, 2019
IOGraphics
Available for: macOS High Sierra 10.13.5
Impact: A local user may be able to read kernel memory
Description: An out-of-bounds read issue existed that led to the disclosure of kernel memory. This was addressed with improved input validation.
CVE-2018-4283: @panicaII working with Trend Micro's Zero Day Initiative
Kernel
Available for: OS X El Capitan 10.11.6, macOS Sierra 10.12.6, macOS High Sierra 10.13.5
Impact: Systems using Intel® Core-based microprocessors may potentially allow a local process to infer data utilizing Lazy FP state restore from another process through a speculative execution side channel
Description: Lazy FP state restore instead of eager save and restore of the state upon a context switch. Lazy restored states are potentially vulnerable to exploits where one process may infer register values of other processes through a speculative execution side channel that infers their value.
An information disclosure issue was addressed with FP/SIMD register state sanitization.
CVE-2018-3665: Julian Stecklina of Amazon Germany, Thomas Prescher of Cyberus Technology GmbH (cyberus-technology.de), Zdenek Sojka of SYSGO AG (sysgo.com), and Colin Percival
Kernel
Available for: macOS High Sierra 10.13.5
Impact: Mounting a maliciously crafted NFS network share may lead to arbitrary code execution with system privileges
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2018-4259: Kevin Backhouse of Semmle and LGTM.com
CVE-2018-4286: Kevin Backhouse of Semmle and LGTM.com
CVE-2018-4287: Kevin Backhouse of Semmle and LGTM.com
CVE-2018-4288: Kevin Backhouse of Semmle and LGTM.com
CVE-2018-4291: Kevin Backhouse of Semmle and LGTM.com

Entry added October 30, 2018
libxpc
Available for: OS X El Capitan 10.11.6, macOS Sierra 10.12.6, macOS High Sierra 10.13.5
Impact: An application may be able to gain elevated privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2018-4280: Brandon Azad
libxpc
Available for: macOS High Sierra 10.13.5
Impact: A malicious application may be able to read restricted memory
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2018-4248: Brandon Azad
LinkPresentation
Available for: macOS High Sierra 10.13.5
Impact: Visiting a malicious website may lead to address bar spoofing
Description: A spoofing issue existed in the handling of URLs. This issue was addressed with improved input validation.
CVE-2018-4277: xisigr of Tencent's Xuanwu Lab (tencent.com)
Perl
Available for: macOS High Sierra 10.13.5
Impact: Multiple buffer overflow issues existed in Perl
Description: Multiple issues in Perl were addressed with improved memory handling.
CVE-2018-6797: Brian Carpenter
CVE-2018-6913: GwanYeong Kim
Entry added October 30, 2018
Ruby
Available for: macOS High Sierra 10.13.5
Impact: A remote attacker may be able to cause unexpected application termination or arbitrary code execution
Description: Multiple issues in Ruby were addressed in this update.
CVE-2017-0898
CVE-2017-10784
CVE-2017-14033
CVE-2017-14064
CVE-2017-17405
CVE-2017-17742
CVE-2018-6914
CVE-2018-8777
CVE-2018-8778
CVE-2018-8779
CVE-2018-8780
Entry added October 30, 2018
Additional recognition
App Store
We would like to acknowledge Jesse Endahl & Stevie Hryciw of Fleetsmith, and Max Bélanger of Dropbox for their assistance.
Entry added August 8, 2018
Help Viewer
We would like to acknowledge Wojciech Reguła (@_r3ggi) of SecuRing for their assistance with four mitigations.
Kernel
We would like to acknowledge juwei lin (@panicaII) of Trend Micro working with Trend Micro’s Zero Day Initiative for their assistance.
Security
We would like to acknowledge Brad Dahlsten of Iowa State University for their assistance.